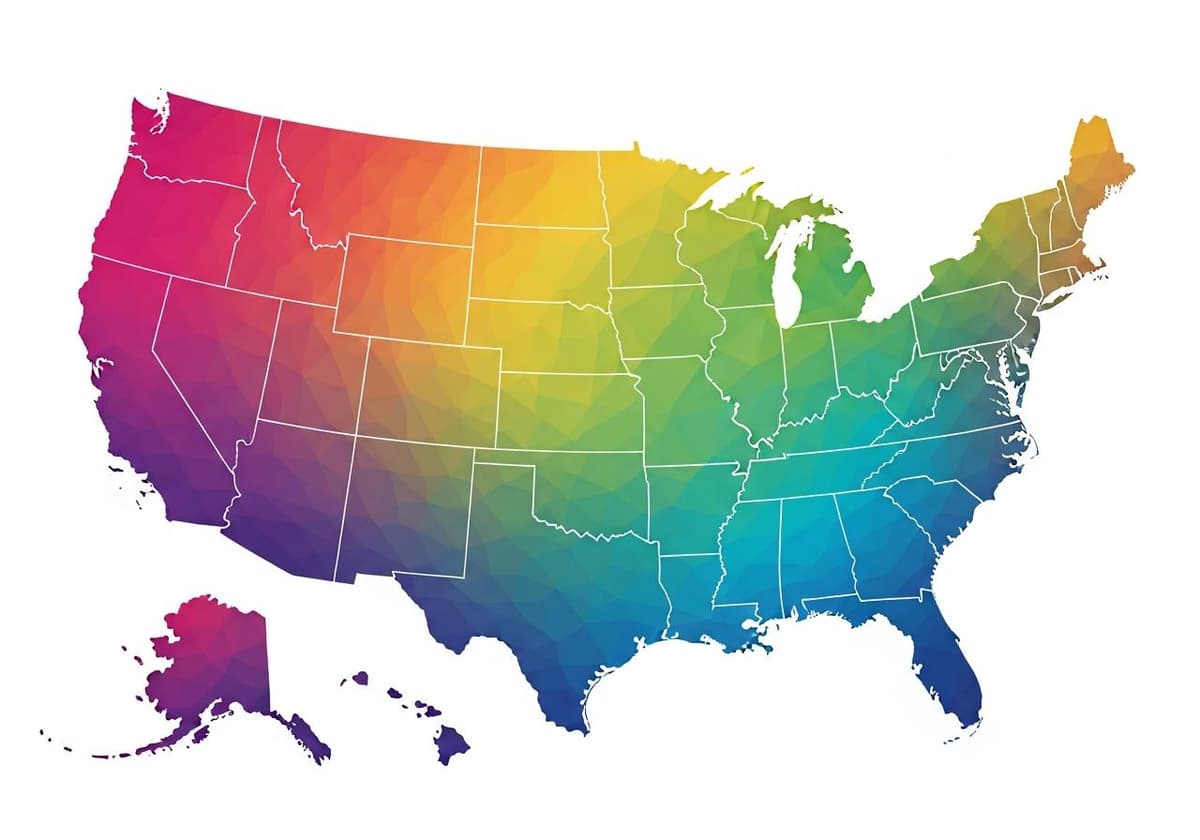
5G Availability By Zip Code
5G is the fifth generation of mobile network technology, succeeding 4G LTE. It's designed to provide faster speeds, improved reliability, and a more robust network for a variety of devices. 5G isn't just faster; it also enables advancements in technology like IoT (Internet of Things), autonomous vehicles, and smart cities. Everyone wants to know about 5G availability by zip code because this determines how easily you can access these powerful advancements in your area.
James Y. Max
December 27, 2025